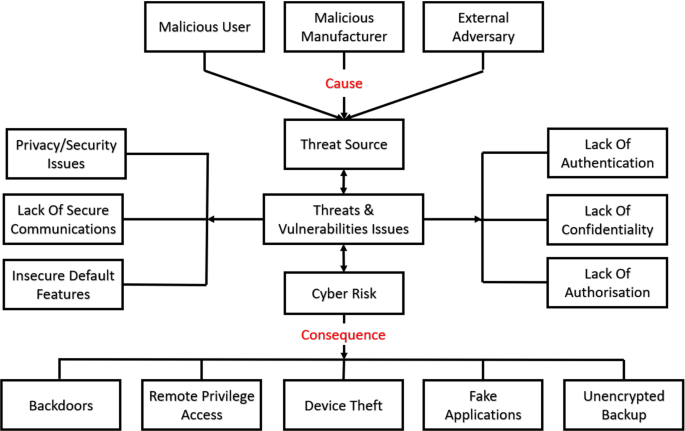
Robotics cyber security: vulnerabilities, attacks, countermeasures, and recommendations | SpringerLink
Robotics cyber security: vulnerabilities, attacks, countermeasures, and recommendations | SpringerLink
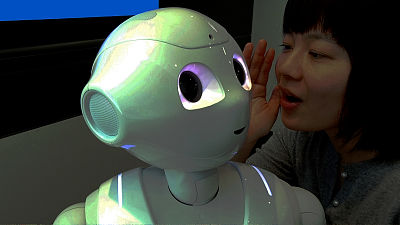
Background Information Privacy Implications For Pepper Robots Effects Solutions References Pepper with a Dash of Salt! - Summary
Robotics cyber security: vulnerabilities, attacks, countermeasures, and recommendations | SpringerLink