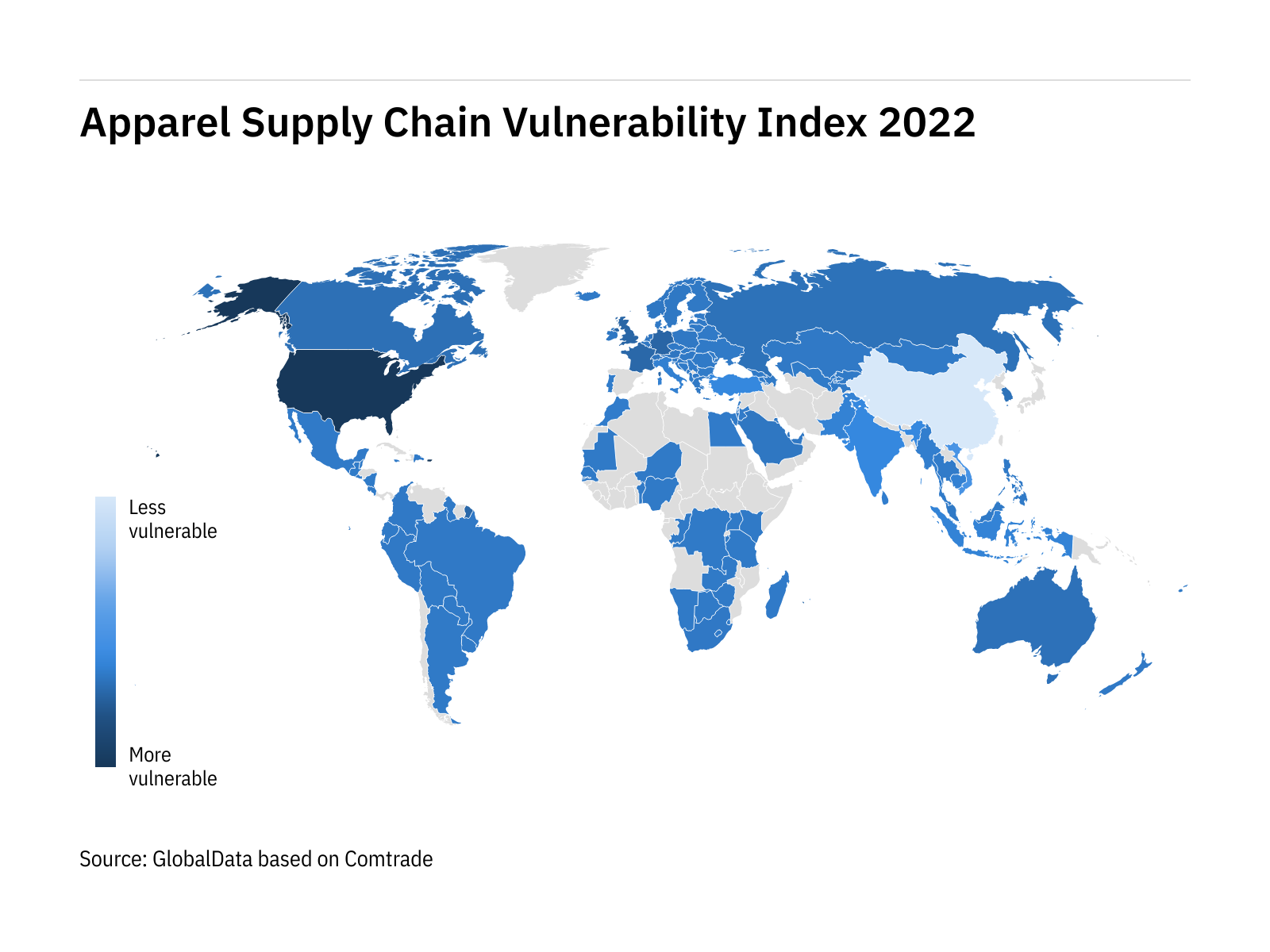
China's resilience shines through in index of world's most vulnerable apparel supply chains - Just Style

Minimizing the vulnerabilities of supply chain: A new framework for enhancing the resilience | Semantic Scholar

Amazon.com: Managing Supply Chain Risk and Vulnerability: Tools and Methods for Supply Chain Decision Makers: 9781848826335: Wu, Teresa, Blackhurst, Jennifer Vincent

Buildings | Free Full-Text | Resilient Capabilities to Tackle Supply Chain Risks: Managing Integration Complexities in Construction Projects
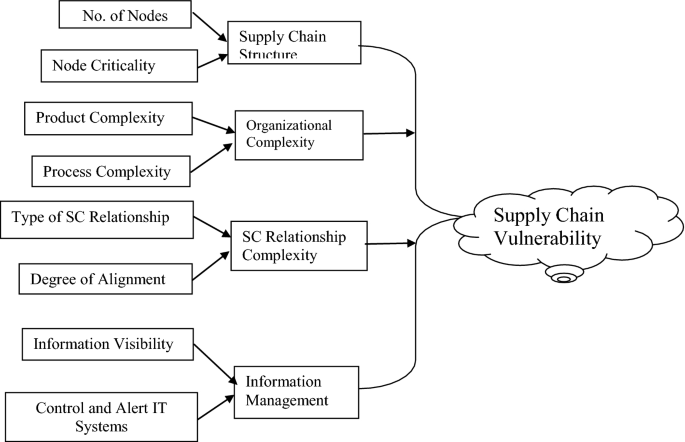









![PDF] Assessing the vulnerability of supply chains using graph theory | Semantic Scholar PDF] Assessing the vulnerability of supply chains using graph theory | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/c50328abeea3d9dea2146af86d1ca90996de067d/3-Figure2-1.png)